Featured Article
Chromebooks. They're not PCs running Windows, they're not Macs, they're not Linux (sorta), they're not Android (except, maybe) ... so what are they?
Well, as it turns out they're ideal for a more-and-more common class of computer user; like my wife, and a close family friend.
I purchased two of them, recently, and Why a Chromebook? (And Why I Purchased Two for the Important People in My Life) has my reasoning and all the details.
Other articles this week
Web pages can be slow for a variety of reasons. Diagnosing a Slow-loading Webpage with Firefox - Introducing the Network Performance Display in Web Developer Tools demonstrates using a tool built into most modern browsers that can help point fingers at possible culprits.
Don't delete an email account until you're positive you won't need it ever again. Will My Email Be There If I Reactivate a Deleted Account? Don't Count On It covers one of many reasons why.
You've probably heard the term "zero day" when it comes to computer vulnerabilities and whatnot. What's a "Zero-Day" Attack? A Diagram of the Vulnerability Timeline explains this confusing bit of "geek speak".
The Ask Leo! Podcast
If you didn't know, Ask Leo! is available as a podcast. So far it's been mostly just me reading, or more correctly narrating each article. That's about to change.
Changes to the Ask Leo! Podcast has the details.
Ask Leo! Live
The most recent Ask Leo! Live last Saturday was fun! I talked about the result of this year's reader survey -- some surprises, some expected, always intersting. Survey Results & More - Ask Leo! Live has the edited video, as well as the full recordings. You'll find notes, a transcript, related links, and of course moderated comments.
The TEH Podcast
Speaking of podcasts, the TEH Podcast has moved on to episode 101!
We discuss some of the slow changes happening in society enabled by technology, due to the pandemic. Gary described a different kind of "dinner out" experience. I discuss my uninterruptible power supply not living up to its name. Virtual graduations are cool, "Nordic Noir", "Mythic Quest", and of course much more.
TEH 101: Cool rockets and TV shows, getting interrupted electronically, and wiping computers..
-
Stay safe. Be well. Be kind.

Featured
Who's Trying to Change My Password? Why It Happens and What to Do
I just happened to check my emails and noticed that I had an email telling me that I had asked for my outlook.com account password to be reset. I had not done this, so I followed the link that confirmed that this was not me. About two minutes later, I received an email from Facebook stating that I had attempted to change my password and was this me? I immediately clicked on the link to report that it wasn't the case. What I'm wondering is if there's any way of finding out how this happened, who's trying to change my password, and the location of who and what was behind this? I checked my session data in Facebook and there were no strange locations there, but then they had failed to log in, so I suppose there wouldn't be. Is anything else of mine at risk? I've checked my bank statement tonight and I am a little worried.
To answer your question, no.
If no one has actually logged into your account, you can't get the information that you're looking for, at least not without a warrant. But I do want to talk about what may have happened in order for you to get that “password has been reset” email. I also want you to do something differently in the future.
Continue Reading: Who's Trying to Change My Password? Why It Happens and What to Do
https://askleo.com/12626
This Week's Articles
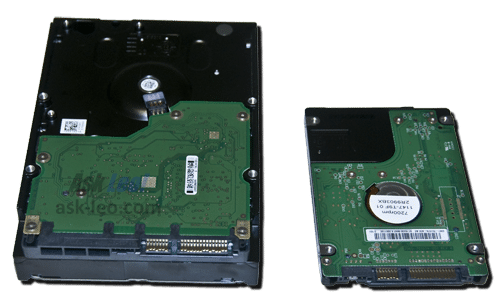
Can I Move My Old Computer's Hard Drive to My New Computer to Transfer Data? My Recommended Approach
A working hard disk formatted for use by any prior version of Windows can certainly be read by Windows versions that come later.
Of course, you'll have to open the box, extract the drive, and do something with it.
Continue Reading: Can I Move My Old Computer's Hard Drive to My New Computer to Transfer Data? My Recommended Approach
https://askleo.com/2424
•
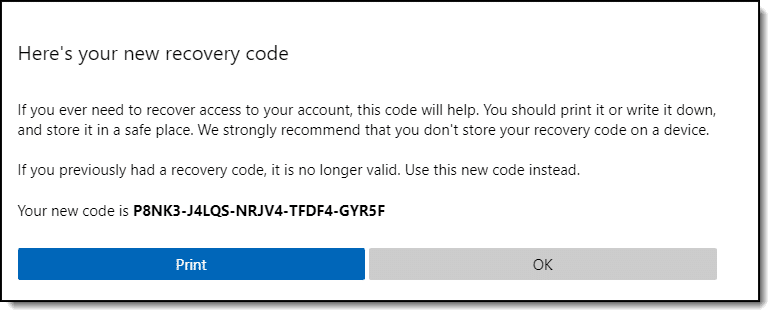
Microsoft Account Recovery Code - What and Why with Instructions Included
A Microsoft recovery code — more correctly, a recovery code for a Microsoft account — is a safety net. It's a huge safety net, in fact. If you haven't already done so, I strongly suggest you create one now.
It didn't dawn on me until recently that these codes are very precious. Having one may be the ultimate proof of Microsoft account ownership.
Continue Reading: Microsoft Account Recovery Code - What and Why with Instructions Included
https://askleo.com/123186
•
5 Steps to Better Wi-Fi In Your House - Improving Your Wireless Connection
The a/b/g/n are all different variations of the 802.11 Wi-Fi protocol. Which gets used is mostly out of your control.
On the other hand, there are definitely several steps that can improve your Wi-Fi performance at home.
Continue Reading: 5 Steps to Better Wi-Fi In Your House - Improving Your Wireless Connection
https://askleo.com/123219
Share Confident Computing!
Love Ask Leo!? Share the love: forward this (without your unsubscribe link at the bottom) to your friends! They'll thank you! (And so will I!)
Did someone forward this to you?
to get your own copy each week. It's FREE! (And there are goodies  .)
.)
For Ask Leo! Patrons
The Ask Leo! Tip of the Day
A feature exclusively available to Ask Leo! Patrons Bronze level & above.
- Tip of the Day: Lock Your Phone
- Tip of the Day: Hacks Aren't About You
- Tip of the Day: Make Print Screen More Useful
- Tip of the Day: Abort Command Prompt Programs with Ctrl+C
More Ask Leo!
Become a Patron
Ask Leo! Books
Facebook -
Twitter -
YouTube -
More..

Leo's Other Projects....
HeroicStories Since 1999, HeroicStories brings diverse, international voices to the world ' reminding us that people are good, that individuals and individual action matter. Stories - new and old - are published twice a week.
Not All News Is Bad - Each day I look for one story in the current news of the day with a positive bent. Just one. And I share it.
leo.notenboom.org - My personal blog. Part writing exercise, part ranting platform, it's where I write about anything and everything and nothing at all.
Newsletter contents Copyright © 2020,
Leo A. Notenboom & Puget Sound Software, LLC.
Ask Leo! is a registered trademark ® of Puget Sound Software,
LLC